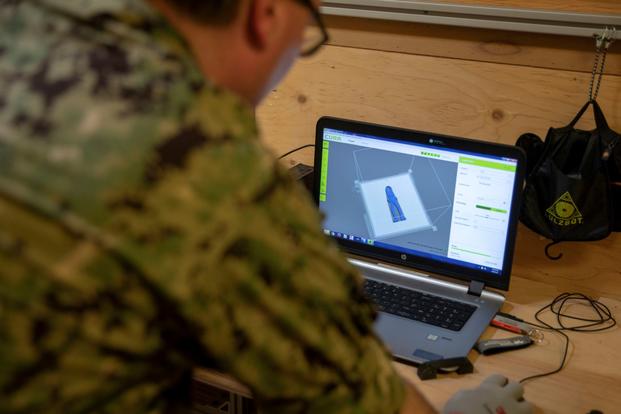
A Pentagon watchdog report warns that the military is not doing enough to secure its 3D printing technology -- an area that the Defense Department and several military branches have touted as "game-changing technology."
The Department of Defense Inspector General's report, released July 1, says that service members are miscategorizing the military's 3D printing programs, formally known as additive manufacturing, or AM, and leaving them vulnerable to cyberattacks.
"Users considered the AM systems as 'tools' to generate supply parts instead of information technology systems that required cybersecurity controls," the report states.
Read Next: Soldier Convicted over Role in Fort Bragg Sham Marriage Ring
It warned that unless the Defense Department properly protects the confidentiality and integrity of its 3D printing systems, hackers "could compromise AM systems to steal the design data or gain access” to DoD networks.
3D printing is starting to be used in major military programs. Early in 2019, an Air Force unit used a printed part to maintain an F-22 Raptor. Around the same time, Marines printed a concrete footbridge. More recently, both the Air Force and Marine Corps touted tools created by service members that have the potential to save money and time across both branches.
The Defense Department's own strategy document on additive manufacturing says the technology will help the military "build a more lethal and ready force" and notes that a key goal is to integrate it into its regular manufacturing.
However, unless properly secured, the new technology could not only be crippled by foreign hackers, it may also give adversaries advantages they didn't have before, according to Peter Singer, a senior fellow at the think tank New America and an expert on cybersecurity and cyberwar.
One issue would be "a foreign attacker stealing your IP [intellectual property], such as a design," Singer told Military.com in an email. "So, they get your hard work and innovation for free and catch up faster -- a specialty of the PLA [China's armed forces]."
There is also the risk that hackers "could alter the information ... such as subtly altering the design or manufacture, so as to compromise it in some way," he added.
Another key problem identified in the report is the ongoing failure to update computer operating systems.
"The need to update operating systems is critical to protecting the AM computers and the printers connected to them," it noted.

The report cited a 2019 incident in which Microsoft issued more than 197 operating system vulnerability fixes. One closed a vulnerability "that allowed attackers to gain unauthorized access to a single computer and then use that access to log into other computers," it said.
The report's authors credited the military for generally making changes following auditor visits, and Singer agreed that the military is doing some things right.
"It is better, by a wide margin, than almost all of the private sector," he said. "But, obviously it is nowhere near where it needs to be, which Pentagon leaders themselves would say."
Outside groups have noted for years that the Pentagon fails to prioritize cybersecurity up front in the acquisition process.
The Inspector General report's recommendations largely focus on ensuring that commands that own 3D printing technology treat it as any other Defense Department information technology system.
Despite disagreement from the Pentagon's chief information officer, or CIO, the commands that were audited -- five in total -- largely agreed with the changes suggested in the report. The CIO argued that the existing policies are adequate; commands simply need to be told that additive manufacturing systems must fall under the existing rules.
Singer said that reports on cybersecurity vulnerabilities will be an ongoing issue.
"Alas, this [report] isn't the first, nor will it be the last," he said.
-- Konstantin Toropin can be reached at konstantin.toropin@military.com. Follow him on Twitter @ktoropin.
Related: A Marine's Invented Truck Tool Is Now Available to Any Unit in the Corps