Hackers released account information belonging to millions of users of the adultery website AshleyMadison.com, including some 15,000 email addresses possibly linked to government and military email addresses, Wired reported Tuesday.
The registered email addresses, as well as the names, addresses and phone numbers submitted by 37 million users of the website that promotes marital affairs, were part of a recent data dump by hackers who stole the sensitive personal information in July, the magazine reported.
The Defense Department couldn't immediately confirm whether the military domains were valid.
"We are aware of the reporting," Army Lt. Col. Joe Sowers, a spokesman at the Pentagon, said on Wednesday in an email. "However, we do not keep service email addresses centrally located. Confirmation of the emails would have to be handled by the services."
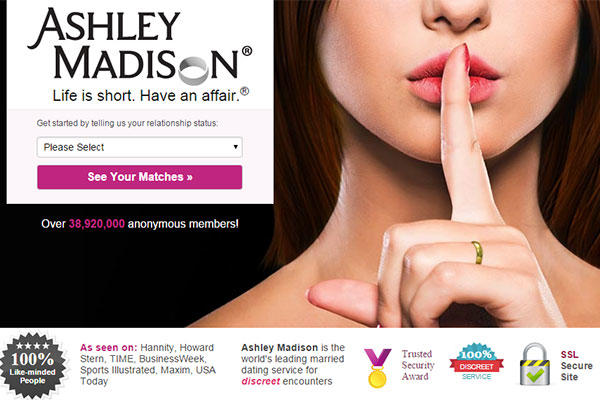
A request seeking comment from a spokesperson for Avid Life Media Inc., which owns AshleyMadison.com -- whose slogan is "Life is Short. Have an Affair" -- wasn't immediately returned. The company on Tuesday condemned the attack, which appears to have been an attempt at moral vigilantism by a hacker group calling itself The Impact Team.
"This event is not an act of hacktivism, it is an act of criminality," the company said in an Aug. 18 statement posted on its website. "It is an illegal action against the individual members of AshleyMadison.com, as well as any freethinking people who choose to engage in fully lawful online activities."
The unofficial analysis of the hacked accounts by the unnamed programmer referenced in the Wired article, who goes by the username "@tx0x0" on Twitter, includes a total of 15,019 email addresses ending in ".mil" or ".gov." Some appear to be suspect, erroneous or outright fake. For example, false domains include "yahoo.mil," "us.ary.mil" and even "fakemail.gov." AshleyMadison doesn't require valid addresses to sign up.
Other addresses appear to be old and likely no longer in use. For instance, 127 addresses are registered to "gimail.af.mil" -- a service phased out by the Air Force in 2010.
However, many domains appear to be very specific and unique to certain military departments. For instance, there were 32 email addresses ending in "cvn74.navy.mil," which is linked to the aircraft carrier the USS John C. Stennis. Indeed, more than 100 addresses were associated with carrier domains alone.
According to the unofficial analysis, the hacked accounts include 6,788 addresses ending in "army.mil" addresses, 1,665 ending in "navy.mil," 809 ending in "usmc.mil" (for U.S. Marine Corps) and 206 addresses ending in the newer domain "mail.mil."
Including the potential civilian domains, the total number of email addresses ending in ".mil" and ".gov" represent about 1 percent of the active-duty end-strength -- and a far smaller share when including Guard and Reserve forces.
Using a .mil email account or computer to access pornography or to register on sites like AshleyMadison.com is prohibited by Defense Department regulations. Violators can be prosecuted under the Uniform Code of Military Justice (UCMJ). Adultery is also punishable under the UCMJ.
-- Brendan McGarry contributed to this report.
-- Amy Bushatz can be reached at amy.bushatz@military.com.